What is a VPN concentrator? Understand its role today
As organizations shift to hybrid and remote models, secure remote access has become a core IT requirement. VPNs are widely used to meet this need by encrypting remote connections and protecting access to internal resources.
However, as organizations scale their VPN deployments, managing user access, performance, and security policies becomes increasingly complex. A VPN concentrator is designed to address these challenges.
In this article, we explain what a VPN concentrator is, how it supports secure remote access, and when organizations may choose it over other VPN technologies.
Understanding VPN concentrators
A virtual private network (VPN) creates a secure, encrypted tunnel over an untrusted network (typically the internet) that allows devices or networks to communicate as if they were on the same private network.
A VPN concentrator is a specialized gateway that works as a central hub for multiple VPN connections. It authenticates users or devices, decrypts incoming VPN traffic, and routes it to the appropriate internal network resources.
VPN concentrators are designed to support a large number of simultaneous VPN connections and are commonly used in remote access VPN deployments, enabling employees to securely access internal systems from remote locations.
VPN concentrators can be implemented as dedicated hardware, software running on servers, firewall devices, or cloud-based VPN gateways.
How VPN concentrators enhance security
VPN concentrators protect network traffic in three main ways:
- Encryption: Transforms data in transit so it can’t be viewed or tampered with by unauthorized parties.
- Authentication: Verifies the identity of users and devices.
- Access controls: Determine which resources an authenticated user can access.
Role of encryption in VPN connections
When a user connects to an organization’s network, the VPN client and concentrator establish a secure tunnel between the user’s device and the concentrator so data can travel safely across the internet. The way this tunnel is created depends on the VPN protocol being used.
In Internet Key Exchange version 2 (IKEv2)/Internet Protocol Security (IPsec) VPNs, IKEv2 handles authentication and securely negotiates encryption keys. Once the keys are established, IPsec uses them to encrypt and protect the data flowing through the tunnel.
In Secure Sockets Layer (SSL)/Transport Layer Security (TLS)-based VPNs, the connection and key exchange are handled via the TLS handshake, the same cryptographic framework that secures HTTPS websites. SSL/TLS VPNs use a different connection process than IKEv2/IPsec, but they serve the same purpose: establishing encrypted communication between the user and the network.
The encryption itself is implemented using algorithms such as 256-bit Advanced Encryption Standard (AES), which is a widely trusted algorithm used to encrypt data.
Many VPN deployments also implement perfect forward secrecy. This feature ensures that even if an encryption key is later compromised, past communications remain secure. It achieves this by generating a unique, temporary key for each session rather than reusing the same key across multiple connections.
User authentication methods
Before a connection is established, a VPN concentrator authenticates the user or device. In other words, it verifies that the person or device is who they claim to be and has permission to access the network.
Common methods of authentication include usernames and passwords, digital certificates, or multi-factor authentication (MFA).
Many VPN concentrators can integrate with enterprise identity providers (IdP) such as Microsoft Entra ID or Okta. This allows organizations to manage user credentials centrally and enforce consistent authentication policies across multiple services, improving both security and administrative efficiency.
Access control and role-based permissions
After a user is authenticated, a VPN concentrator enforces access control, determining which network resources the user can access. This prevents users from accessing sensitive systems or data to which they don’t have permission.
Many VPN concentrators support role-based access control (RBAC), which allows administrators to assign permissions based on a user’s role or group within the organization. For example, a finance employee might have access to accounting servers, whereas a marketing employee might not. This simplifies management, reduces the risk of accidental exposure, and ensures that access policies are applied consistently across the organization.
Benefits of using a VPN concentrator
VPN concentrators offer several advantages for organizations that need to manage secure remote access at scale.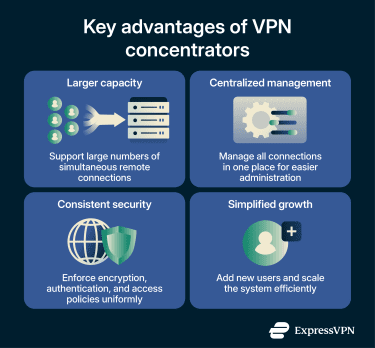
Enhanced network security
Traditional secure remote access relies on VPN client software installed on each user’s device to establish encrypted tunnels to a VPN gateway, where authentication and access policies are enforced.
Most VPN concentrators rely on VPN client software installed on user devices. Some also offer browser-based (clientless) SSL VPN portals for clientless access. However, these portals are typically limited to web-based applications and don’t provide full network-layer access like a traditional VPN client.
By centralizing remote connections through a concentrator, organizations can enforce security policies consistently, reduce the risk of misconfiguration, and give administrators a single point to monitor and respond to potential threats.
Scalable remote access solutions
VPN concentrators are typically designed to handle thousands of remote users simultaneously, far more than a typical small-office VPN router designed for limited remote connections.
Centralizing all connections in a single system makes it easier to manage growth, as administrators can add new users and adjust resources in a single place rather than configuring each connection individually.
Additionally, since VPN concentrators are designed for enterprise-scale remote access, they often include features to support both performance at scale and reliability. For example:
- Load balancing: Distributes VPN connections across multiple devices to prevent any single concentrator from becoming overloaded.
- Hardware acceleration: Specialized hardware that speeds up encryption and decryption, maintaining high performance for large volumes of traffic.
- High-availability setups: Standby devices that automatically take over if the primary concentrator fails, ensuring continuous uptime.
- Clustering: Multiple concentrators working together to share load and provide redundancy.
Applications of VPN concentrators in business
Below are some of the practical problems that VPN concentrators help organizations solve.
Implementing secure remote access
Remote employees need to connect to corporate networks to access internal resources such as file servers, intranets, and collaboration tools. The problem is that organizations have limited control over where or how employees connect.
If they connect to the corporate network from unsecured public networks, such as those often used at coffee shops, airports, or home Wi-Fi, sensitive information, including login credentials and company files, can be put at risk.
A VPN concentrator addresses this problem by encrypting the traffic between remote users and the corporate network and centralizing authentication and access control.
Dynamic IP address management
Remote employees may connect from different locations or networks. This makes it difficult for organizations to control access, enforce consistent policies, or track who is doing what on the network, because users' source IP addresses and network locations are constantly changing.
A VPN concentrator solves this problem by assigning each remote user an internal, virtual IP address from an organization-controlled pool. This makes remote users appear as part of the internal network, allowing systems, firewalls, and monitoring tools to apply familiar IP-based rules.
Additionally, concentrators handle IP assignment dynamically. Each remote user is automatically assigned an available internal IP from the pool when they connect, and that IP is returned to the pool when they disconnect.
These features allow new or returning users to join the network seamlessly, without requiring IT staff to manually assign addresses. They also help keep the network organized, even as the number of remote users grows or fluctuates throughout the day.
Managing network traffic and load
As the number of remote users grows, the volume of VPN connections can strain a network. Without proper management, this can lead to slower connections, bottlenecks, or service interruptions, directly impacting the productivity of remote employees.
A VPN concentrator manages this load by handling all remote connections in a centralized system designed to handle many users simultaneously and distribute traffic efficiently. This keeps performance stable even during peak usage periods and helps ensure a reliable experience for everyone.
Mechanisms commonly supported by VPN concentrators to manage traffic and maintain performance at scale include:
- Traffic inspection: Examines data flowing through VPN tunnels to identify unusual patterns or enforce security and usage policies.
- Quality of Service (QoS): Prioritizes critical applications, such as video calls or Voice over Internet Protocol (VoIP), to maintain smooth performance during high traffic.
- Session management: Tracks individual VPN sessions to allocate resources efficiently and maintain stable connections for all users.
- Monitoring and logging: Provides administrators with insights into network activity, helping troubleshoot issues and support security auditing.
Comparison of VPN technologies
Organizations have multiple options for providing secure remote access. In the sections below, we examine some VPN concentrator alternatives.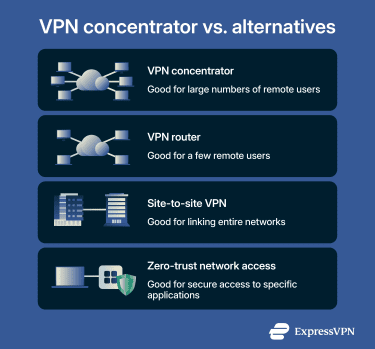
VPN concentrator vs. VPN router
While VPN concentrators and VPN routers share some features, they are designed for different scales and use cases.
Differences in functionality
Both VPN routers and VPN concentrators encrypt traffic and authenticate users, keeping remote connections private.
One key difference is centralization. A VPN concentrator consolidates all remote connections into a centralized device or service, enabling organizations to enforce consistent security policies, monitor and log activity, and manage users more efficiently. This centralized approach also makes it easier to handle network growth, dynamically assign IP addresses, and maintain reliable performance as the number of remote users increases.
Concentrators are also designed to support many more simultaneous connections than typical VPN routers. They efficiently manage high volumes of traffic, provide enterprise-grade monitoring and reporting capabilities, and are optimized to scale with the needs of large remote workforces.
Cost implications
The main disadvantage of VPN concentrators compared to VPN routers is cost. They’re typically more expensive to implement due to the use of enterprise-grade hardware and licensing requirements. For this reason, they may not be worth it for organizations that don’t need to support large numbers of simultaneous remote connections.
VPN concentrator vs. site-to-site VPN
Site-to-site VPNs are designed to connect entire networks together. For example, an organization might use it to link a branch office to corporate headquarters. Devices at either site can then communicate securely as if they were on the same network. Site-to-site VPNs are typically persistent connections between gateways and are optimized for network-to-network traffic rather than individual users.
In contrast, concentrators are primarily designed to handle remote-access VPNs. They typically focus on connecting individual remote users and are better suited for distributed workforces.
While some concentrators can also support site-to-site tunnels, their architecture and features are optimized for managing large numbers of concurrent remote users rather than connecting entire networks.
VPN concentrator vs. zero-trust network access (ZTNA)
Zero-trust network access (ZTNA) is an alternative approach to remote access that focuses on application-level access control. Instead of granting users broad access to an internal network after authentication (as many VPN concentrators do), ZTNA provides access only to specific applications or services based on identity, device posture, and policy rules.
While VPN concentrators typically create a secure tunnel into the corporate network, ZTNA solutions operate on a “least privilege” model, granting users access only to the exact resources they need, rather than the entire network. This can reduce the risk of lateral movement if an account is compromised.
VPN concentrators are still widely used and effective, particularly in environments that require full network access. However, organizations adopting a zero-trust security model may choose ZTNA as a more granular alternative for remote access. Note: The term “gateway” can describe the function of routing and terminating VPN traffic, which is why a concentrator is sometimes called a gateway.
A VPN concentrator is a centralized system designed to handle many VPN connections at once, providing centralized authentication, access control, and management for large organizations. While all concentrators use VPN technology, not all VPNs require a concentrator.
FAQ: Common questions about VPN concentrators
What is the difference between a VPN gateway and a concentrator?
How does a VPN concentrator impact network security?
When should a business consider investing in a VPN concentrator?
What is the difference between a VPN and a VPN concentrator?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN